From Cloud Exposure to Identity-Governed Action: Oasis Joins the Wiz Integration Network (WIN)
Cloud security is entering its next operating model.
Not because teams lack visibility. Because automation is now the default: workloads, pipelines, services, and emerging AI agents are constantly shipping new access paths. And the blast radius is no longer a single resource. It’s the non-human identities behind access: service principals, workload identities, API keys, and secrets powering production.
That's why Oasis Security is joining the Wiz Integration Network (WIN) as a certified partner.
Wiz pioneered horizontal security; breaking down silos between code, cloud, and runtime to deliver unified exposure visibility. With Wiz Exposure Management now GA, teams can prioritize exposures based on true impact and accelerate remediation across complex environments. Oasis is the identity control plane for the Agentic Access era, governing non-human identities and the AI agents that depend on them. Together, we're extending horizontal security to the identity layer, so teams can move from "we see it" to "we can act safely."
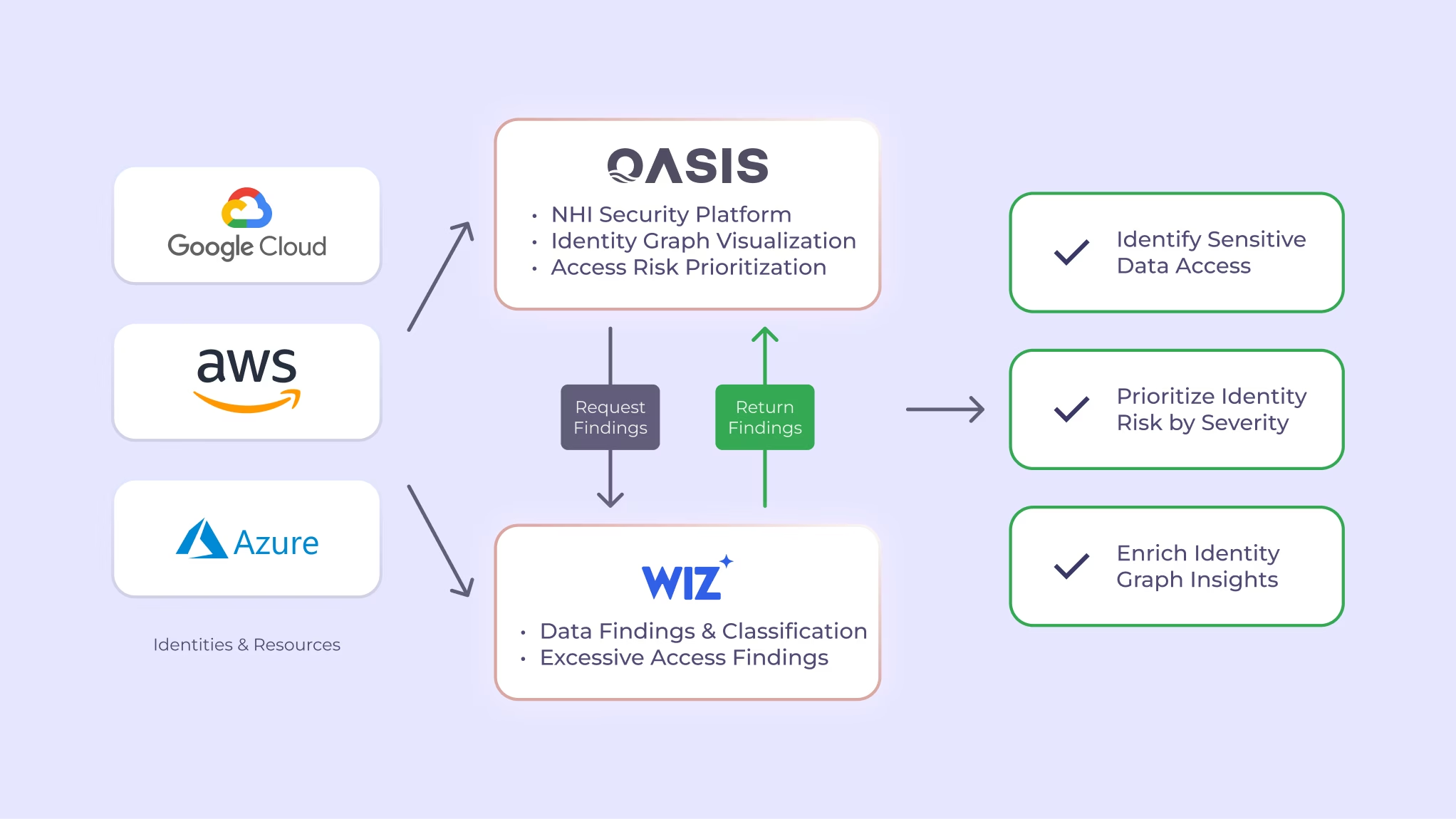
The Oasis Security integration with Wiz enables joint customers to drive end-to-end remediation, governance, and lifecycle management for Non-Human Identities (NHI), and the AI agents and services that depend on them. By enriching the Oasis platform with Wiz issues and DSPM findings, customers gain deep context into NHI privilege, usage, and ownership, more effectively surfacing and prioritizing risk. This allows closing the loop on remediation and lifecycle management actions such as hygiene and safe key rotation.
Why this partnership matters
Security teams are already prioritizing exposures. The real bottleneck is safe identity change. When a finding lands, teams still need to answer:
- Which non-human identity is behind access?
- What privilege does it have, and is it actually used?
- Who owns it?
- Can we rotate or right-size safely?
That last mile is where risk lingers, not due to lack of effort, but because identity-driven remediation can’t be guesswork in production.
AI agents are compounding the problem
Every agentic system ships with NHIs that operate continuously, autonomously, and across trust boundaries. Wiz's own AI-SPM research makes the point clearly: agentic AI doesn't introduce exotic attacks, it amplifies familiar ones. Over-privileged identities. Excessive data access. Unclear ownership.
The same pattern Oasis sees across every enterprise: AI agents amplify identity risk at machine speed. Without governance, that risk compounds faster than teams can respond.
What the integration delivers
Once configured, Oasis ingests Wiz Issues and DSPM findings into the Oasis identity graph; correlating cloud exposure and data sensitivity to the non-human identities behind access.
In plain terms: teams can see when identities have access to sensitive resources (severity/category/type), understand blast radius through privilege and usage, identify owners, and then drive governance and lifecycle actions with confidence.
Two practical use cases
- Issues: from Wiz signal to NHI action: By enriching Oasis with Wiz Issues, teams gain deeper context around NHI resources, entitlements, exposure, and risk; so they can prioritize by true blast radius and drive lifecycle actions like hygiene and safe key rotation.
- DSPM: focus on the highest-consequence access paths: By ingesting Wiz DSPM findings, Oasis can surface and prioritize risks tied to sensitive access, helping security teams focus on the highest-consequence exposures and govern the identities behind them.
Bottom line
Wiz finds exposure and sensitive data risk with clarity and speed. Oasis brings control and identity-governed remediation, so teams can prioritize by blast radius and close the loop with safe lifecycle governance in production.
- Mutual Wiz customer? Contact Oasis to enable the integration in your environment.
- Want a walkthrough? Book a demo to see Wiz findings in the Oasis identity graph.
- Just curious? Explore at the join solution brief.
We do newsletters, too
Discover tips, technical guides and best practices in our biweekly newsletter.


