What Are Non-Human Identities (NHIs) and Why Are They Risky?

Non-human identities (NHIs) have become an essential component of modern IT environments. As enterprises adopt cloud-native architectures and automation grows, NHIs are proliferating rapidly. According to Rubrik Zero Labs, non-human identities now outnumber human users by 45 to 1 in the modern enterprise, with some organizations seeing ratios as high as 100 to 1.
Despite their importance, NHIs often remain unmanaged or poorly secured, creating gaps that attackers can exploit. Understanding what these identities are, the roles they serve, and how to secure them is critical for any organization managing hybrid or multi-cloud services infrastructures.
In this article, we will define NHIs, examine their types, explore the challenges they pose, and outline best practices for managing non-human identities and improving security measures.
What are Non-human Identities?
A non-human identity (NHI) is a digital construct used for machine-to-machine access and authentication across on-prem, cloud and edge environments.
Unlike human identities, which are tied to individual users and typically secured through multi-factor authentication (MFA), Single Sign-on (SSO), and behavioral oversight, NHIs operate autonomously (often at scale), created programmatically, often by developers or IT systems, and rely on credentials such as API keys, service accounts, certificates, OAuth tokens, or SSH keys. This distinction makes securing NHIs a unique challenge, requiring different approaches than those used for human identity security.

Examples of Non-Human Identities
Examples of NHIs include Service Accounts, System Accounts, Application Accounts, and Machine Identities. Authentication methods for NHIs vary, incorporating secret information and federation mechanisms. Examples of authentication methods for NHIs encompass Secrets, Keys, Access keys, Certificates, and Tokens, each serving specific purposes in secure communication and authorization.
Special considerations arise in scenarios where identities are inseparable from the authentication string, as seen in Storage account access keys, Shared Access Signatures (SAS) tokens, and API keys for Software as a Service (SaaS) applications like Snowflake. In such instances, the authentication methods encapsulates permissions configuration, complicating identity and access management (IAM) and identity access governance (IGA). As organizations continue to automate business processes with AI, the growth of Non-Human Identities is expected to accelerate, underscoring their critical role in the evolving landscape of enterprise systems.
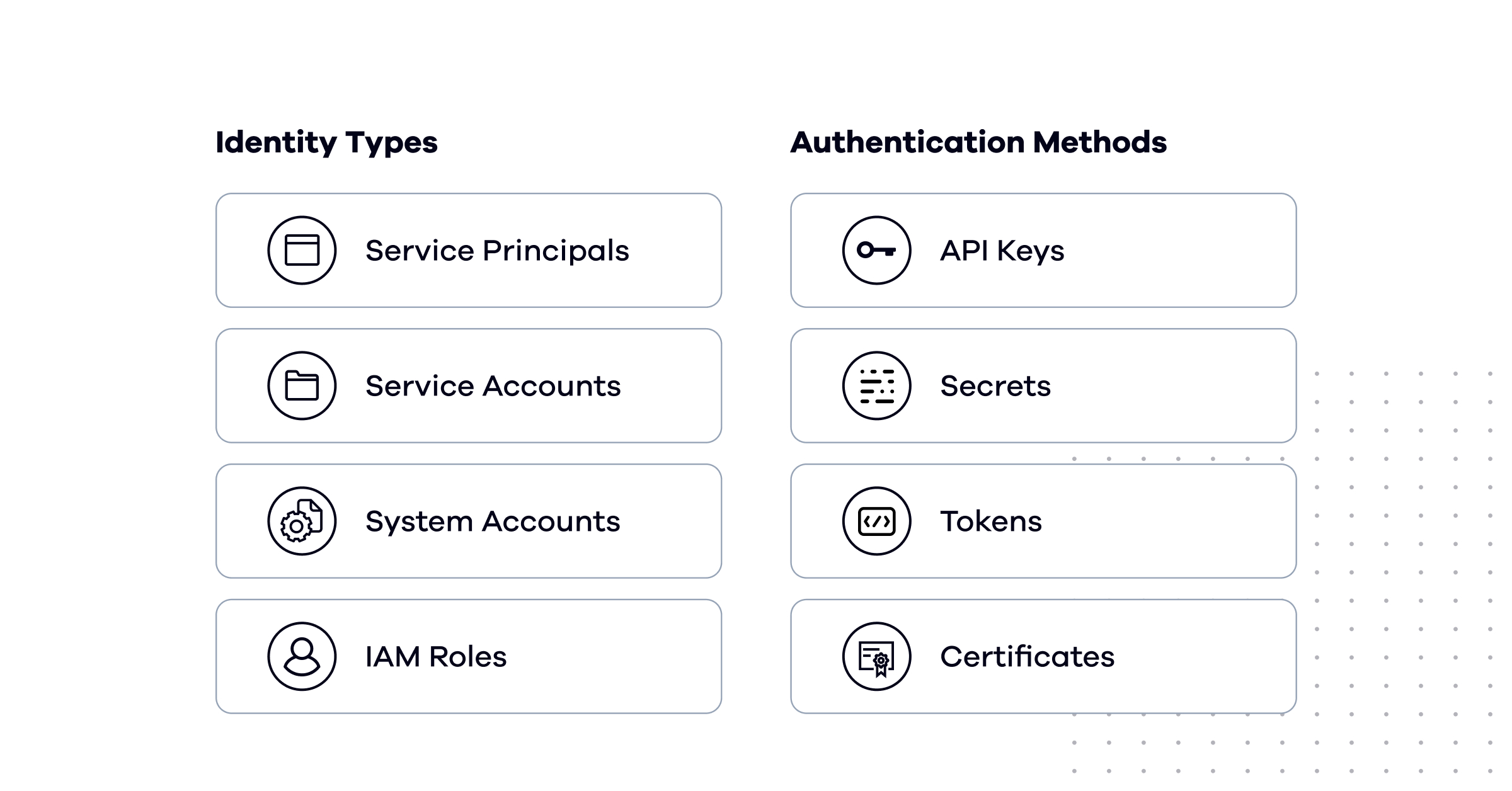
Examples of NHIs include service accounts, system accounts, application accounts, and machine identities. Authentication methods for NHIs vary, incorporating secret information and federation mechanisms. Examples of authentication methods for NHIs encompass secrets, keys, access keys, certificates, and tokens, each serving specific purposes in secure communication and authorization.
Special considerations arise in scenarios where identities are inseparable from the authentication string, as seen in storage account access keys, Shared Access Signatures (SAS) tokens, and API keys for Software as a Service (SaaS) applications like Snowflake. In such instances, the authentication method encapsulates permissions configuration, complicating identity and access management (IAM) and identity access governance (IGA). As organizations continue to automate business processes with AI, the growth of non-human identities is expected to accelerate, underscoring their critical role in the evolving landscape of enterprise systems.
Service Accounts: Service accounts are used by applications to interact with other systems or services. For example, a web application might use a service account to access a database or connect to a payment gateway.
Service Principals: A Service Principal is an NHI used by applications, services, or automated workflows to authenticate and access resources in cloud environments. Unlike human users, Service Principals operate without direct user interaction and are secured through credentials such as client secrets or certificates.
System Accounts: A system account is similar to a service account and is created by an operating system typically with a high level of privileges. A local system account is used to conduct tasks and perform actions on a device or server.
IAM Roles: An IAM role is a type of identity within AWS with a fixed set of entitlements and permissions allowing users to access resources and perform actions in AWS. These entities are not bound to a human user but can be taken on by other non-human identities with temporary credentials that last for the session.
API Keys: API keys enable machine-to-machine authentication, often used by IoT devices or for integrating applications with external APIs. They serve as credentials that grant access to specific services or functionalities.
Machine Identities in Cloud Workloads: Machine identities represent entities like virtual machines (VMs), containers, or serverless compute services. These identities allow cloud workloads to authenticate and communicate securely within an environment. Machine identities have grown from 50,000 per enterprise in 2021 to 250,000 in 2025, representing a 400% increase—further highlighting their critical role in modern infrastructures.
Tokens and Certificates: Tokens and certificates are critical for securing authentication and encryption between applications. Short-lived tokens, such as OAuth tokens, are often preferred due to their temporary nature, which reduces the risk of misuse. Certificates, like TLS certificates, ensure secure communication between systems.
Additional examples of NHIs and their associated credentials include:
- Storage Access Keys: Credentials that grant access to cloud storage services, often with broad permissions and no expiration by default.
- Database Users: Application-level credentials used to query and modify data in production databases.
- Personal Access Tokens (PATs): Developer-generated tokens used to authenticate API requests, frequently with long lifespans and wide scope.
- SAS Tokens: Time-limited tokens that grant granular access to Azure storage resources, though misconfiguration can expose sensitive data.

Human Identities vs. Non-human Identities
NHIs differ significantly from human identities in key aspects:
- Decentralization: NHIs are not centrally managed like human identities; instead, they are created and managed across multiple platforms by various stakeholders. It can be a real challenge to classify if a user is a human or a machine.
- Ownership: Unlike human identities, NHIs are not tied to specific individuals, evading regulatory requirements and often used by multiple administrators or applications.
- Scale: the large volume of NHIs (10x-50x more than human) creates a massive attack surface that is growing exponentially
- Rate of change: NHIs are subject to frequent creation and deprecation, aligning with the rapid pace of code evolution, rendering them more challenging to govern. However, it's worth noting that NHIs can also persist unchanged for years without rotation or imposed consumer limitations.
- Developer driven: unlike with human identities, the creation and control of NHIs aren’t centralized to IT or Identity Team. In many cases, NHIs are directly created by developers or even citizen developers in no-code low-code who may not be aware of their usage, as they represent the only means for the code they need to interact with systems
- Secret expiration: while frequent password rotation is very common around privileged users, many of the NHI are set to live for a very long time, and sometimes even without an expiration date.
- Operational Risk: Engaging with NHIs carries inherent operational risks. In the absence of a comprehensive understanding of all consumers, there is a potential for disrupting production systems. Moreover, efforts to rotate secrets may unintentionally disrupt established and vital business workflows.
- Authentication Diversity: NHIs support multiple authentication methods, reflecting technological evolution. Various systems may employ different authentication methods, leading to a wide range of approaches in use. The basic concept of human identity security relies on the fact that you can use these three factors to secure the authentication: 1) something you know (for example, password) 2) something you are (for example, face recognition) 3) something you have (for example, mobile phone) and then do multi-factor authentication. With NHIs the only protection is the secret that the user (in most cases a developer) gave to the machine - there is no SSO or MFA in the middle. This means that if attackers get hold of a Service Account and the secret there isn’t anything else that can stop them. In the cloud era, where APIs are the gatekeepers of access, identity becomes the new perimeter; especially when sensitive information is handled by machines.
What Are the Biggest Security Risks of Non-Human Identities?
Non-human identities introduce significant security risk because they often operate with long-lived credentials, excessive privileges, and limited oversight. Unlike human users, NHIs do not authenticate through MFA, do not benefit from behavioral monitoring, and rarely have clear ownership—making them ideal targets for attackers.
One of the most common risks is credential sprawl. API keys, service account secrets, and tokens are frequently created for a specific project and then forgotten, remaining active for years without rotation. Over time, these credentials accumulate broad permissions that exceed their original purpose. If compromised, they provide attackers with persistent, automated access to sensitive systems.
Another major risk is lack of visibility. Many organizations cannot confidently answer which applications use a given service account, what actions it performs, or whether it is still required. This uncertainty leads teams to avoid rotation or decommissioning out of fear of breaking production, allowing risk to persist indefinitely.
The business impact is significant. According to IBM's 2025 Cost of a Data Breach Report, the global average cost of a data breach is $4.44 million, while U.S. organizations face an average cost of $10.22 million—an all-time high. The report specifically recommends implementing strong operational controls for non-human identities to reduce credential abuse, recognizing NHI security as a mainstream enterprise priority.
Recent incidents illustrate how NHI vulnerabilities translate into real-world exposure:
- Microsoft AI Storage Breach: A misconfigured SAS token exposed 38TB of sensitive internal data, including passwords and private keys.
- CircleCI Breach: Attackers compromised an OAuth token, forcing thousands of customers to rotate secrets across their environments.
- Mercedes-Benz Breach: Unauthorized access to internal systems occurred due to mismanaged service accounts with excessive privileges.
These cases share a common thread: credentials that were over-permissioned, under-monitored, or never rotated became the entry point for attackers.
At scale, these issues dramatically expand the attack surface. As APIs become the primary access layer for data and infrastructure, unsecured NHIs effectively become unguarded entry points into critical systems.
How Attackers Exploit Non-Human Identities
Attackers increasingly target non-human identities because they offer high-impact access with minimal resistance. Unlike human accounts, NHIs do not trigger suspicious login alerts, MFA challenges, or user-reported anomalies, allowing malicious activity to remain undetected for long periods.
A common entry point is exposed credentials. API keys and secrets are frequently leaked through public code repositories, CI/CD logs, misconfigured storage buckets, or third-party integrations. Once obtained, these credentials can be used immediately—often without any additional verification.
Attackers also exploit over-privileged service accounts. Many NHIs are granted broad permissions to “avoid friction” during development. When compromised, these identities enable lateral movement across cloud services, data stores, and SaaS platforms, accelerating breach impact.
In cloud environments, attackers may abuse workload identities to move between compute resources or escalate privileges by chaining roles and permissions. Because activity originates from a “legitimate” machine identity, it blends into normal traffic patterns.
These attacks are particularly dangerous because they are silent and automated, persisting until credentials are manually discovered and revoked—often long after damage has occurred.
Why Legacy IAM and PAM Tools Fail for Non-Human Identities
Traditional IAM and PAM solutions were designed around human identity assumptions and struggle to manage non-human identities at modern scale. As a result, many organizations attempt to force NHIs into systems that were never built for them.
IAM platforms typically rely on HR-driven lifecycle events—joiners, movers, and leavers—to govern access. Non-human identities do not follow this model. They are created programmatically, owned by applications rather than people, and change as code evolves. This makes accurate ownership assignment, certification, and deprovisioning extremely difficult.
PAM tools, while effective for protecting privileged human access, often focus on credential storage rather than usage context. They may vault secrets, but they lack insight into how those secrets are used, what they connect to, or whether access is still required. This limitation makes safe rotation and least-privilege enforcement operationally risky.
As environments grow more automated and API-driven, these gaps become more pronounced. Without identity models built for machine behavior, organizations are left with fragmented visibility, manual processes, and persistent risk concentrated in their non-human workforce.
How to Secure Non-Human Identities
Securing non-human identities requires a fundamentally different approach than human identity management. Organizations that treat NHIs as an extension of their existing IAM programs will continue to face visibility gaps and unmanaged risk. Effective NHI security requires purpose-built strategies across four key areas.
Enforce least privilege by default. NHIs should be provisioned with the minimum permissions required for their function—nothing more. Broad access granted during development must be scoped down before production deployment, and permissions should be reviewed regularly as application requirements evolve.
Establish ownership and accountability. Every NHI should have a clearly assigned owner responsible for its lifecycle. Without ownership, credentials persist indefinitely because no one has authority—or incentive—to rotate or decommission them. Ownership should transfer automatically when applications change hands or teams are restructured.
Automate credential rotation. Long-lived secrets are among the most exploited attack vectors. Organizations should implement automated rotation policies and prioritize short-lived credentials wherever possible. Where rotation is operationally risky, invest in dependency mapping to understand what will break before making changes.
Monitor behavior continuously. NHIs generate predictable activity patterns. Deviations—such as a service account accessing unfamiliar resources or authenticating from unexpected locations—should trigger alerts. Behavioral baselines allow security teams to detect compromise even when credentials remain valid.
Integrate NHI governance into the development lifecycle. Security teams cannot govern what they cannot see. NHI creation should be visible to security from the start, with guardrails embedded into CI/CD pipelines and cloud provisioning workflows. Governance applied retroactively will always lag behind the pace of development.
Align NHI governance with Zero Trust principles. Zero Trust assumes no identity—human or machine—should be trusted by default. Every NHI must be authenticated, authorized, and continuously verified before accessing resources. Without visibility and control over non-human identities, Zero Trust architectures remain incomplete.
For a complete framework on auditing, certifying, and governing non-human identities across your organization, see our Comprehensive Guide to Non-Human Identity Management.
Conclusion
Non-human identities are now foundational to how enterprises operate—but they have also become one of the largest unmanaged risks in modern environments. As NHIs continue to proliferate across cloud, SaaS, and AI-driven workflows, organizations need dedicated strategies and tools to discover, govern, and secure them at scale.
Our mission is to empower enterprises to reduce the risks associated with unmanaged NHIs, maintain compliance, and simplify identity governance. Request a Demo to explore how Oasis Security can transform your approach to non-human identity management.
Frequently Asked Questions
A service account that allows a web application to connect to a database is a common example of a non-human identity. Other examples include API keys used by integrations, OAuth tokens that authorize third-party applications, IAM roles assumed by cloud workloads, and certificates that secure machine-to-machine communication.
Human identities are tied to individual users and protected through interactive authentication methods like passwords, MFA, and SSO. Non-human identities are assigned to applications, services, and machines. They authenticate programmatically using credentials such as API keys, tokens, and certificates without human intervention or behavioral oversight.
NHIs often operate with long-lived credentials, excessive permissions, and no clear ownership. Unlike human accounts, they cannot use MFA and do not trigger typical security alerts. These characteristics make them attractive targets for attackers seeking persistent, undetected access to critical systems.
Securing NHIs requires enforcing least privilege, assigning clear ownership, automating credential rotation, and monitoring for anomalous behavior. Organizations also need visibility into where NHIs exist, what they access, and whether they are still required capabilities that traditional IAM and PAM tools were not designed to provide.
Machine identities are digital credentials assigned to physical or virtual infrastructure, servers, IoT devices, virtual machines, and cloud instances. Workload identities are a subset of machine identities, specifically used by applications and services to authenticate and interact with other systems. Both fall under the broader category of non-human identities and require dedicated security controls.
We do newsletters, too
Discover tips, technical guides and best practices in our biweekly newsletter.



